AMIS implemented a hierarchical variant of threshold signatures, using different levels/ranks in its distributed key generation (DKG) and signing logic, based on a previous research paper.


AMIS implemented a hierarchical variant of threshold signatures, using different levels/ranks in its distributed key generation (DKG) and signing logic, based on a previous research paper.

We are besieged by simple problems…. Checklists can provide protection Atul Gawande, The Checklist Manifesto: How to Get Things Right Checklists are a simple yet

Zcash is a decentralized, open-source cryptocurrency that provides strong privacy protections thanks to state-of-the-art cryptographic components. Zcash will upgrade its protocol to a new version,

Beam-mw is a confidential cryptocurrency based on the MimbleWimble protocol, which is MimbleWimble is a cryptographic construction based on the Pedersen commitments and elliptic-curve cryptography.Beam-mw
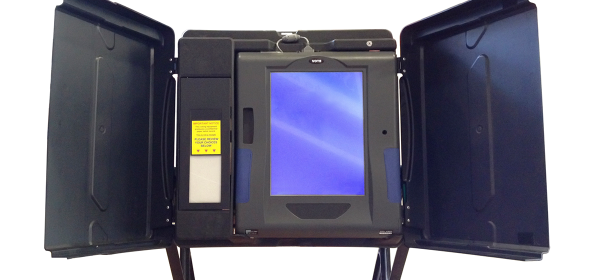
“It’s not the voting that’s democracy; it’s the counting.” —Tom Stoppard For cryptography researchers, e-voting isn’t about voting machine or online voting, but is

IOHK is an engineering company that builds cryptocurrencies and blockchains for academic institutions, government entities, and corporations. Major projects of IOHK are Ethereum Classic, the Daedalus wallet, and the Cardano platform.