Written by Yann Lehmann and Harish Segar of the Kudelski Security Threat Detection & Research Team
Summary
On July 11th, Microsoft disclosed a remote code execution (RCE) vulnerability affecting Windows and Office product, CVE-2023-36884, with a CVSS score of 8.3. At the time of writing the vulnerability is unpatched, exploited and Microsoft is investigating the next steps.
Microsoft reads, “An attacker could create a specially crafted Microsoft Office document that enables them to perform remote code execution in the context of the victim. However, an attacker would have to convince the victim to open the malicious file.“
This implies that user interaction is required before the RCE. Also, Crowdstrike confirmed that they have detection and prevention logic that targets those behaviours and Microsoft stated that customers with Microsoft Defender for Office are protected from attachments that attempt to exploit this vulnerability.
Affected Applications
Microsoft suggested that the following applications would be impacted:
- Excel.exe
- Graph.exe
- MSAccess.exe
- MSPub.exe
- Powerpnt.exe
- Visio.exe
- WinProj.exe
- WinWord.exe
- Wordpad.exe
Technical Details
The technical details of the vulnerability are not extremely detailed publicly but they leverage an abuse of URL handlers native to Microsoft Windows by crafting specific documents from the list of affected applications.
Temporary workarounds and mitigations
Microsoft recommends the following workarounds. While these compensating controls can mitigate exploitation, they could also affect regular functionality for certain use cases related to these applications. Therefore, it’s important to test before deploying changes widely.
- Leverage attack surface reduction rule to block all office applications from creating child processes
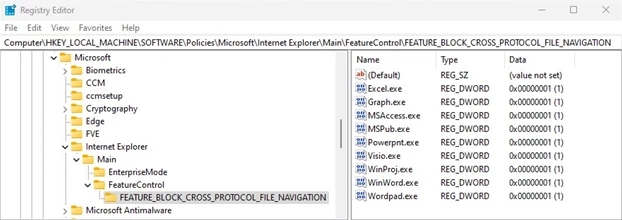
- Set the FEATURE_BLOCK_CROSS_PROTOCOL_FILE_NAVIGATION registry key to 1 for the affected applications to avoid exploitation.
You can use the following PowerShell code to edit the registry keys.
$registryPath = "HKLM:\SOFTWARE\Policies\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BLOCK_CROSS_PROTOCOL_FILE_NAVIGATION"
$applications = @("Excel.exe", "Graph.exe", "MSAccess.exe", "MSPub.exe", "PowerPnt.exe", "Visio.exe", "WinProj.exe", "WinWord.exe", "Wordpad.exe")
if (!(Test-Path -Path $registryPath)) {
New-Item -Path $registryPath -Force | Out-Null
}
foreach ($app in $applications) {
Set-ItemProperty -Path $registryPath -Name $app -Value 1 -Type DWord
}Because user interaction is required, the best is to raise awareness of your users towards that risk, so they do not interact with malicious samples.
Detection Guidance
The earliest samples were writing Word documents to disk with a .url extension, which can be used because it is uncommon.
Observations showed that fully exploited payloads were also writing strange RTF, CHM or ZIP files to disk which can also be hunted on.
What the Cyber Fusion Center (CFC) is doing
The CFC is investigating the possibility of a threat hunting campaign to identify successful exploitation of this vulnerability, using internal queries and methodology available for our clients. You will see it appear in your customer portal as soon as it is launched.
Sources
- https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-36884
- https://www.reddit.com/r/crowdstrike/comments/14y1yei/20230712_situational_awareness_microsoft_office/
- https://learn.microsoft.com/en-us/microsoft-365/security/defender-endpoint/attack-surface-reduction-rules-reference?view=o365-worldwide#block-all-office-applications-from-creating-child-processes
- https://www.microsoft.com/en-us/security/blog/2023/07/11/storm-0978-attacks-reveal-financial-and-espionage-motives/