Introduction
ZigBee is an open-source wireless technology used in low-powered embedded devices (radio systems) to facilitate efficient and effective machine-to-machine communication (typically 10-100 meters apart) while keeping the costs low. ZigBee is built on IEEE 802.15.4 standard and is supported by the ZigBee Alliance (a consortium of companies aiming to standardize the ZigBee Protocol). The ZigBee Alliance has three network specifications: ZigBee Pro, ZigBee RF4CE, and ZigBee IP. The ZigBee Alliance also publishes application profiles like ZigBee Home Automation, ZigBee Smart Energy, etc. to allow different device classes to interoperate.
This post explores the available network topologies of ZigBee protocol, its stack layout, and logical devices that are central to a ZigBee network. An understanding of the general components of a ZigBee protocol is critical to performing ZigBee security analysis and pentesting.
Protocol Stack Overview
The ZigBee protocol stack consists of four layers – Physical layer, Medium access control (MAC) layer, Network layer (NWK) and Application layer (APL) – as shown in Figure-1 below. Each layer provides a set of services exposed to the upper layer via a service access point. The physical and MAC layers are governed by IEEE 802.15.4 standard and the network and application layers are governed by the ZigBee standard. In gist:
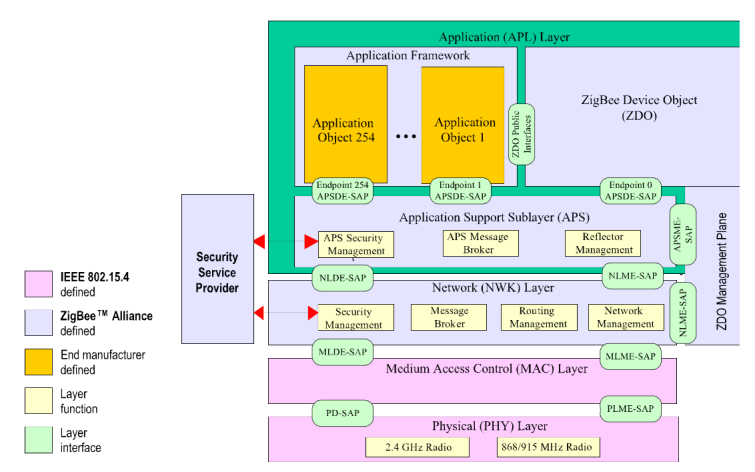
The Application layer (APL)
It consists of ZigBee device objects (ZDOs), Application support sub-layer (APS), and the Application Framework.
- ZigBee Device Objects (ZDO) are applications which employ network and application support layer primitives to implement ZigBee End Devices, ZigBee Routers, and ZigBee Coordinators. It provides an interface between the application objects, the device profile, and the APS. The ZDO is responsible for initializing the APS, NWK, and the Security service provider. It assembles configuration information from the end applications to determine and implement device and service discovery, security management (key loading, key establishment, key transport and authentication), network management (network discovery, leaving/joining a network, resetting a network connection and creating a network), binding, node, and group management. ZigBee Device Object (ZDO) manages the security policies and the security configuration of a device. Objects listed as mandatory in the specifications document reside on all ZigBee devices.
- The APS provides an interface between the NWK and APL. It provides services for the establishment and maintenance of security relationships. Services are provided via APS data entity (APSDE: provides data transmission services between application entities) and APS management entity (APMSE: provides security services, binding of devices and group management). The APS layer allows frame security to be based on link keys or the network key. The APS layer is responsible for the processing steps needed to securely transmit outgoing frames, securely receive incoming frames, and securely establish and manage cryptographic keys. Upper layers control the management of cryptographic keys by issuing primitives to the APS layer.
- Application Framework is the environment in which application objects are hosted (up to 254 can be defined). These are usually manufacturer defined application objects. It defines application profiles (agreements for messages, message formats, and processing actions that enable developers to create an interoperable, distributed application employing application entities that reside on separate devices) and clusters.
Network Layer (NWK)
The network layer ensures correct operation of the IEEE 802.15.4-2003 MAC sub-layer and provides a suitable service interface to the application layer. It interfaces with application layer via data entity (NLDE: generates network level PDU, provides topology-specific routing and security) and the management entity (NLME: configures a new device, starts a network, performs joining, rejoining and leaving a network functionality, provides addressing capabilities, neighbor discovery, route discovery, reception control and routing). The NWK layer is responsible for the processing steps needed to securely transmit outgoing frames and securely receive incoming frames. The NWK layer’s frame-protection mechanism uses the Advanced Encryption Standard (AES) and CCM* (Enhanced counter with CBC-MAC mode of operation) for authentication and confidentiality.
MAC Layer
The MAC layer’s responsibilities include controlling access to radio channel via CSMA-CA mechanism, transmitting beacon frames, synchronization, and providing a reliable transmission mechanism. There are four types of MAC frames: data frames, beacon frames, acknowledgment frames, and MAC command frames. This layer’s security is based on the IEEE 802.15.4 standard augmented with CCM* to provide encryption and integrity capabilities only. CCM is an enhanced counter with CBC-MAC mode operation encryption scheme. The upper layers set the MAC layer default key to that of the active network key and the MAC layer link key to any link key from the upper layer.
Physical Layer
It operates in two separate frequency ranges: 868/915 MHz and 2.4 GHz. The physical layer is responsible for packet generation, packet reception, data transparency, and power management.
ZigBee Functional Descriptors
ZigBee Device Object defines three types of logical devices, each having a specific role as illustrated (Figure 2):
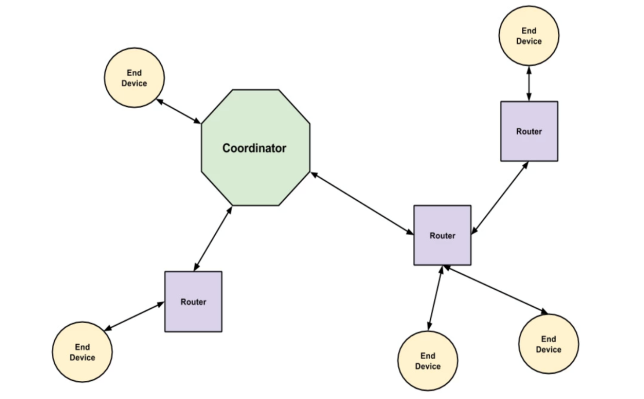
- ZigBee Coordinator: is a device responsible for establishing, executing, and managing the overall ZigBee network. It is responsible for configuring the security level of the network and configuring the address of the Trust Center (The default value of this address is the ZigBee coordinator’s own address, otherwise, the ZigBee coordinator may designate an alternate Trust Center). The ZigBee coordinator also maintains a list of currently associated devices and facilitates support of orphan scan and rejoin-processing to enable previously associated devices to rejoin the network. There is only one coordinator per network and hence, it can never be put to sleep (It is possible for no coordinator to be present in the network). The coordinator can also double-up as router as required.
Note: ZigBee Trust Center is an application that runs on the device trusted by other devices within the ZigBee network to distribute keys for the purpose of network and end-to-end application configuration management. The Trust center could be the coordinator device or a device designated as the Trust center by the coordinator the Zigbee Network.
All members of the network recognize exactly one Trust Center, and there is exactly one Trust Center in each secure network. It is configured to operate in either standard or high security mode and may be used to help establish end-to- end application keys either by sending out link keys directly (that is, key-escrow capability) or by sending out master keys. These keys are generated at random.
- Standard mode: designed for residential applications. In this mode, the Trust Center maintains a list of devices, master keys, link keys and network keys with all the devices in the network; however, it maintains a standard network key and controls policies of network admittance. In this mode, each device that joins the network securely shall either have a global link key or a unique link key depending upon the application in use. It is required that the trust center have prior knowledge of the value of the link key and the type (global or unique) in order to securely join the device to the network.
- A global link key has the advantage that the memory required by the Trust Center does not grow with the number of devices in the network.
- A unique link key has the advantage of being unique for each device on the network and application communications can be secured from other devices on the network.
Both types of keys may be used on the network, but a device shall only have one type in use per device-key pair
- High security mode: designed for high security commercial applications. In this mode, the Trust Center maintains a list of devices, master keys, link keys and network keys that it needs to control and enforce the policies of network key updates and network admittance. It also mandates the implementation of key establishment using SKKE and entity authentication.
- ZigBee Router: is an intermediate node device responsible for routing packets between end devices or between an end device and the coordinator. Routers need the Trust Center’s permission to join the network if security is enabled on the network and can also double-up as end devices. At certain occasions, routers can allow other routers and end devices to join the network and will maintain a list of currently associated devices and facilitate support of orphan scan and rejoin processing to enable previously associated devices to rejoin the network. Since routers link multiple sections of a network, they cannot be put to sleep.
- ZigBee End Device: is usually a sensor node device that monitors and collects environment data. End devices are low powered or battery operated unlike routers or coordinators. Hence, they can be put to sleep for a certain period of time to conserve energy when there is no activity to be monitored provided a router or a coordinator is not doubling up as an end device. End devices can neither route traffic or permit other nodes to join the network in general, provided a router or a coordinator is not doubling up as an end device.
Network Topologies
ZigBee supports three types of personal area network (PAN) topologies and the choice of topology must take into consideration which nodes are line-powered or battery-powered, expected battery lifetime, amount of network traffic required, latency requirements, the cost of the solution, etc. Zigbee topologies include:
Star: In this topology (Figure 3), there are no routers and the coordinator is responsible for routing the packets in the network, initiating, and maintaining the devices on the network. End devices can communicate only via the coordinator.
Drawback: single point of failure. Failure of the coordinator can shut-down the whole network. The star hub can become bottlenecked with network bandwidth.

Tree: in this topology (Figure 4), the coordinator acts as the root node responsible for establishing the network and choosing certain key network parameters. A router can be a child to the coordinator or another router and is responsible for moving data and control messages through the network using hierarchical routing strategy. An end device can be a child to a coordinator or a router and can communicate to another end device only via a router or a coordinator. Tree networks may employ beacon-oriented communication as per the IEEE 802.15.4 standard.
Drawback: Children nodes become unreachable if their parent node shuts-down.

Mesh: also called as a self-healing topology (Figure 5) allows full peer-to-peer communication. It has a single coordinator, multiple routers to extend the network, and optional end devices. The coordinator is responsible for establishing the network and choosing certain key network parameters. In this topology, routers can double-up as end devices but, cannot emit beacons. As it is self-healing, failure of a coordinator does not result in a single point of failure and is the least vulnerable to link failure.
Drawback: complex and difficult to setup and is a major overhead on the nodes.

Note: ZigBee standard does not support cluster tree topology like 802.15.4 standard.
Conclusion
The popularity of ZigBee protocol has grown in leaps and bounds over the years. In parallel, security attacks on ZigBee –enabled devices has grown incrementally as well. Its adoption in personal home and hospital care, commercial building automations, etc. begs to assess the security of the ZigBee protocol where a hack on a critical device such as the pacemaker can be life threatening. This article provides an overview of the ZigBee protocol and its network components, a knowledge that serves as a pre-requisite to understanding ZigBee security and pentetsing. For further information regarding Network setup and other related functions, please refer to the Zigbee Specification document. Next post, ZigBee Security: Basics (Part 2) explores the security features provided by the ZigBee standard.
References
[1] ZigBee Specification Document 053474r20. Provided by ZigBee Alliance.
[2] Figure 2: https://mmbnetworks.atlassian.net/wiki/spaces/SKB/pages/39518242/Zigbee+Network+Concepts
[3] Figure 3: http://vlssit.iitkgp.ernet.in/ant/ant/10/theory/
[4] Figure 4: http://www.informit.com/articles/article.aspx?p=1409785&seqNum=4
[5] Figure 5: https://www.certsi.es/en/blog/security-zigbee-communications


