UPDATE “BadRabbit/Diskcoder.D” OCT 24, 2017:
Summary
On 24 October 2017, BadRabbit/DiskCoder.D, a variant of Not-Petya, was discovered affecting Russia, Ukraine, Bulgaria, and other countries across Europe and Asia. This new variant leverages hard coded credentials, credential theft, and Windows administrative shares to spread across the local network. BadRabbit also attempts to infect WebDav servers using stolen credentials (such as Exchange severs) and lacks the ability to spread via the EternalBlue exploit which made its predecessor, Not-Petya, so effective.
The Cyber Fusion Center’s initial analysis has revealed that this attack is a new combination of pre-existing delivery, download, open source encryption tools, and ransomware messages. The initial infection vector is likely waterhole attacks and drive-by downloads. Once the machine is initially infected, the Diskcoder.D ransomware begins spreading the ransomware to other machines on the local network.
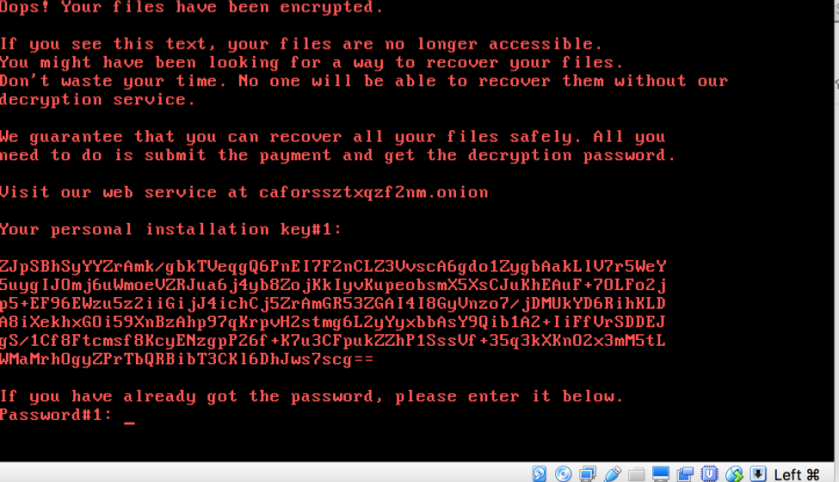
Kudelski Security has confirmed that DiskCoder.D does not upload the encryption keys to the attackers, as such, it’s likely not possible for the ransomware authors to actually decrypt files for any victims that have been impacted. Kudelski Security highly recommends that impacted victims do not make any ransom payments.
Kudelski Security continues to see attacks of this nature targeting different verticals and seemingly beginning in Europe. This most recent example comes on the heels of recent warnings from European and US based security groups, including Kudelski Security, about this kind of threat activity.
Description
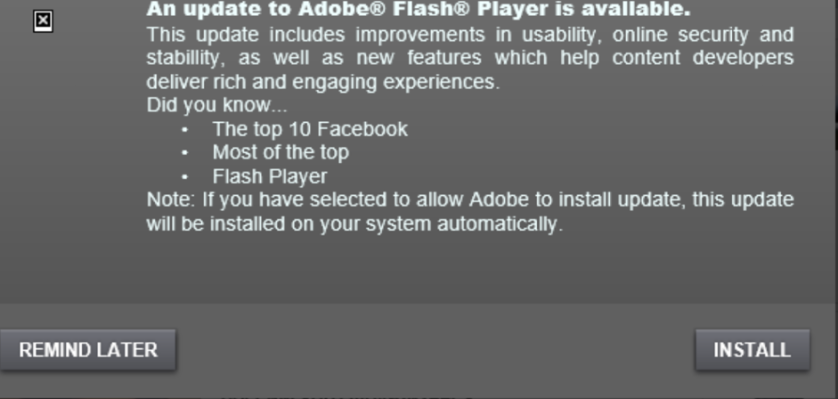
The BadRabbit ransomware is likely delivered via a waterhole or drive-by attack as a fake Adobe Flash Player update. Users are encouraged to download and run the executable by a pop-up warning them that an Adobe Flash Player update is available:
Once the malware is executed, it attempts to steal credentials from infected machines using MimiKatz. BadRabbit then attempts to identify other machines on the same local subnet by performing an Address Resolution Protocol (ARP) scan. Once additional potential victims have been identified, BadRabbit attempts to leverage the stolen and hard coded credentials to mount remote SMB shares on the target systems, copy, and execute the ransomware on those targets. Additionally, BadRabbit attempts to use WebDav to upload and execute the ransomware onto WebDav enabled systems (such as Microsoft Exchange).
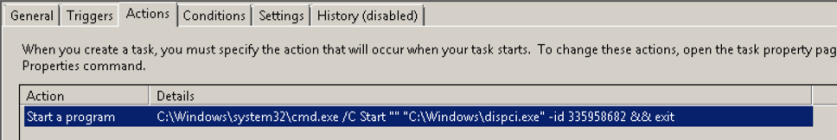
At the same time as BadRabbit is scanning the network for additional victims, the ransomware creates two scheduled tasks on the machine:
- Drogon – Created to reboot the machine
- Rhaegal – Starts the encryption process once the machine reboots
Once BadRabbit has located additional victims on the local network and attempted to execute its malicious payload, a reboot occurs and the computer begins to encrypt the local drive. Encryption is performed using the legitimate and popular open source DiskCryptor software and is triggered via the “Rhaegal” scheduled task mentioned earlier.
The ransomware includes the following hard coded credentials (all username and passwords combinations are attempted):
| Usernames | Passwords |
| Administrator | Administrator |
| Admin | administrator |
| Guest | Guest |
| User | guest |
| User1 | User |
| user-1 | user |
| Test | Admin |
| root | adminTest |
| buh | test |
| boss | root |
| ftp | 123 |
| rdp | 1234 |
| rdpuser | 12345 |
| rdpadmin | 123456 |
| manager | 1234567 |
| support | 12345678 |
| work | 123456789 |
| other user | 1234567890 |
| operator | Administrator123 |
| backup | administrator123 |
| sus | Guest123 |
| ftpuser | guest123 |
| ftpadmin | User123 |
| nas | user123 |
| nasuser | Admin123 |
| nasadmin | admin123Test123 |
| superuser | test123 |
| netguest | password |
| alex | 111111 |
| 55555 | |
| 77777 | |
| 777 | |
| qwe | |
| qwe123 | |
| qwe321 | |
| qwer | |
| qwert | |
| qwerty | |
| qwerty123 | |
| zxc | |
| zxc123 | |
| zxc321 | |
| zxcv | |
| uiop | |
| 123321 | |
| 321 | |
| love | |
| secret | |
| sex | |
| god |
Remediation Recommendations:
Kudelski Security highly recommends that clients leverage client firewalls to block SMB inbound on end-user machines and desktops. Additionally, Kudelski Security recommends that client’s limit the number of users who have local administrative access to end-user machines. Limiting administrative access to end-user machines would prevent credential theft attempts and the creation of scheduled tasks, thus preventing encryption by this ransomware.
Kudelski Security also recommends that clients with Windows 10 Enterprise enable the operating system’s Credential Guard feature (https://docs.microsoft.com/en-us/windows/access-protection/credential-guard/credential-guard) to prevent credential theft attempts from occurring, even by malware which runs with administrative permissions.
Clients should also enable Windows 10’s Controlled Folder Access features (https://docs.microsoft.com/en-us/windows/threat-protection/windows-defender-exploit-guard/controlled-folders-exploit-guard) to prevent ransomware from making changes to or encrypting data stored in controlled folders.
Clients with network based intrusion detection systems (IDS) should look for alerts such as “GPL NETBIOS SMB-DS repeated logon failure” or similar alerts in order to identify potential attempts by BadRabbit to use hard-coded credentials to mount SMB shares.
The Kudelski Security Cyber Fusion Center has already performed hunting for BadRabbit/Diskcoder.D on behalf of our Threat Monitoring and Endpoint Detection and Response clients. The Cyber Fusion Center will create security incident’s if any suspicious or malicious activity is identified as part of this ransomware campaign.
The Cyber Fusion Center will continue to work with our vendor partners to ensure all managed and monitored technology is updated to detect this threat.
Sources
https://www.welivesecurity.com/2017/10/24/kiev-metro-hit-new-variant-infamous-diskcoder-ransomware/
https://securelist.com/bad-rabbit-ransomware/82851/
Indicators
Install_flash_player.exe (Dropper): de5c8d858e6e41da715dca1c019df0bfb92d32c0
Mimikatz (32-bit): 413eba3973a15c1a6429d9f170f3e8287f98c21c
Mimikatz (64-bit): 16605a4a29a101208457c47ebfde788487be788d
Infpub.dat DLL (spreader & encryption): 79116fe99f2b421c52ef64097f0f39b815b20907
Discpi.exe (lockscreen): afeee8b4acff87bc469a6f0364a81ae5d60a2add
Payment site: hxxp://caforssztxqzf2nm[.]onion
Inject URL: hxxp://185.149.120[.]3/scholargoogle/
Distribution URL: hxxp://1dnscontrol[.]com/flash_install.php
List of compromised sites being used to distribute the fake Adobe Flash Player update:
- hxxp://argumentiru[.]com
- hxxp://www.fontanka[.]ru
- hxxp://grupovo[.]bg
- hxxp://www.sinematurk[.]com
- hxxp://www.aica.co[.]jp
- hxxp://spbvoditel[.]ru
- hxxp://argumenti[.]ru
- hxxp://www.mediaport[.]ua
- hxxp://blog.fontanka[.]ru
- hxxp://an-crimea[.]ru
- hxxp://www.t.ks[.]ua
- hxxp://most-dnepr[.]info
- hxxp://osvitaportal.com[.]ua
- hxxp://www.otbrana[.]com
- hxxp://calendar.fontanka[.]ru
- hxxp://www.grupovo[.]bg
- hxxp://www.pensionhotel[.]cz
- hxxp://www.online812[.]ru
- hxxp://www.imer[.]ro
- hxxp://novayagazeta.spb[.]ru
- hxxp://i24.com[.]ua
- hxxp://bg.pensionhotel[.]com
- hxxp://ankerch-crimea[.]ru
PREVIOUS UPDATE JUNE 30, 2017:
- Microsoft Windows 10 Enterprise includes a feature called “Credential Guard”. This feature can prevent certain attacker tools from compromising administrative credentials using well known techniques such as a Pass the Hash attack. Having this feature enabled would have prevented NotPeya from harvesting local credentials to spread within a local network (one of the methods used by the worm component). More Information: below:
- https://docs.microsoft.com/en-us/windows/access-protection/credential-guard/credential-guard
- https://mva.microsoft.com/en-us/training-courses/deep-dive-into-credential-guard-16651?l=pdc37LJyC_1204300474
- https://blogs.technet.microsoft.com/mmpc/2017/06/29/windows-10-platform-resilience-against-the-petya-ransomware-attack/
- Microsoft is also releasing a new feature for Windows 10 in September/October which enables certain files and folders and should provide end users and enterprises another tool to protect against ransomware. This feature is being called “Controlled Folder Access”. More Information:
- The malcode used to create the installation ID which would presumably then be used to create a customized decryption key for each victim was randomly generated and useless. Kudelski Security reiterates: DO NOT PAY THE RANSOM.
UPDATE: 5:30 P.M. EST
As we often see in these global outbreak and response scenarios, information can change quickly. The following are a few updates based on what we’ve learned since our initial advisory.
- The ransomware is not actually petya.a. It does use some its components but the malcode used in today’s attacks was built to look like petya instead
- There does appear to be a kill switch in this first variant that stops the local encryption. The malcode looks for a copy of itself in C:\windows. The file name has been identified as perfc.dat. Unfortunately, it still appears to attempt its spread across the network.
- There are reports that “patient zero” is a finance technology company based in Ukraine
- We have seen reports of thousands of devices compromised within a just a few minutes at several different organizations
- CVE-2017-0199 is not part of this malcode. It was mentioned early on as related but was likely a misattribution due to near simultaneous detections of different attacks
- General steps of the infection
- ARP Scan
- Check/Get credentials (mimikatz or similar)
- Psexec to execute WMI
- If psexec fails use eternalblue
- Reboot to encrypt
- If clients can catch the reboot before it completes, it has been reported that files can be saved by not turning on the computer and recovering files offline.
- We urge caution when looking for some the common IOC’s that have been released so far. Some of them will generate high volumes of false positive alerts, in particular those related to CVE-2017-0199 (see #5)
- The malcode used a fake MS certificate and XOR to avoid most of the current AV detection routines.
- DO NOT PAY the ransom. The email associated with the bitcoin wallet is not valid.
- This attack and the code associated with it is far more professional and dangerous than what we saw WannaCry.
- Expect to see new and creative ways that attackers can automate propagation of malcode through an environment.
The following breaking information is subject to change as new data continues to pour into the CFC Threat Monitoring group.
Kudelski Security’s Cyber Fusion Center’s initial analysis has revealed that this attack is a new combination of pre-existing delivery, download, and malware/ransomware components. The initial infection vector is likely via phishing email or via the network (neither confirmed). Once the machine is initially infected, the Petyawrap’s worm component begins spreading the ransomware to other machines on the local network via several different methods, including the Equation Group’s EternalBlue exploit (similar to WannaCry). However, this worm is also leveraging PSEXEC (a way to remotely manage computers) and Windows Management Instrumentation (WMI) to infect machines already patched against EternalBlue.
Reference:
- https://research.kudelskisecurity.com/2017/05/18/the-equation-groups-post-exploitation-tools-danderspritz-and-more-part-1/
- https://research.kudelskisecurity.com/2017/05/13/security-advisory-wcry2-ransomware-outbreak/
Once a machine is initially exploited (either via EternalBlue or WMI), the worm begins to install the Petya Ransomware variant (https://securelist.com/petrwrap-the-new-petya-based-ransomware-used-in-targeted-attacks/77762/), which then restarts the affected endpoint and begins the encryption process. It’s important to note that the ransomware is leveraging vulnerabilities that were patched by Microsoft in March and built in Windows functions (such as WMI and PSEXEC) to spread. The usage of WMI and PSEXEC makes this worm effective against machines that may have already been patched against EternalBlue and other exploits. This ransomware variant has successfully automated the usage of highly effective methods traditionally used by advanced attackers to silently move laterally within a network by remotely executing code.
This variant can easily spread through the network because it lacks a Wannacry like “kill switch” to slow it’s spread.
Due to the usage of both the EternalBlue exploit and built in Windows management functions (WMI), the Cyber Fusion Center recommends that clients take the following actions:
- Disable inbound SMB on all external firewalls
- Disable inbound SMB connections using the built-in windows endpoint firewalls
- Disable SMBv1 for all endpoints and severs in the organization
- Fully patch all Windows systems
- Ensure that employees are not local administrators on domain joined machines (used to spread the worm via WMI and PSEXEC without exploits)
- If PSEXEC and WMI is not strictly controlled within the environment, it is highly advisable to temporarily disable WMI (Note: This may impact legitimate administrative tools such as SCCM, disable WMI with extreme caution)
Other outlets reporting details (rapidly evolving):
https://twitter.com/danielgallagher/status/879713478361182208
https://twitter.com/mikko/status/879703285321674752
https://twitter.com/payloadsecurity/status/879701663040319493
https://twitter.com/ankit5934/status/879681380686340096
https://twitter.com/mikko/status/879702057829138433
https://www.theverge.com/2017/6/27/15879480/petrwrap-virus-ukraine-ransomware-attack-europe-wannacry
https://twitter.com/0x09al/status/879702450038599681
https://twitter.com/gossithedog/status/879734018039836672
Our previous high-level recommendation:
Organizations must review and evaluate their vulnerability and patch management programs to ensure confidence, comprehensiveness, and effectiveness. Security patches are a fundamental and critical foundation of any organizations security program and should be tested and applied quickly. Organizations should also perform a “health checkup” and review backup strategies, test backups regularly, and ensure backups are easily accessible while also being protected from encryption and deletion. Additionally, organizations should be looking to implement strick controls to limit the usage Windows tools commonly used by attackers such as PSEXEC and WMI.
The CFC will continue to monitor client’s environments for indicators or this variant.
If you have questions or concerns please reach out to the CFC at [email protected] or call the CFC hotline (regional based, refer to the Client Portal for your number.)


One comment