Unmanned Aerial Vehicles (UAVs) offer new perspectives, both from a civilian and a military standpoint; yet, they present vulnerabilities having the potential to lead to disastrous consequences regarding public safety if exploited successfully, as evidenced by recent hacks. These repercussions can be prevented by implementing best practices, continuously assessing the technologies used and most importantly by remaining aware of the environment, of the weaknesses that may be exploited and of the threats that may emerge. The purpose of this article is not to provide countermeasures or solutions, but to outline flaws and vulnerabilities to better understand and address potential threats and threat actors.
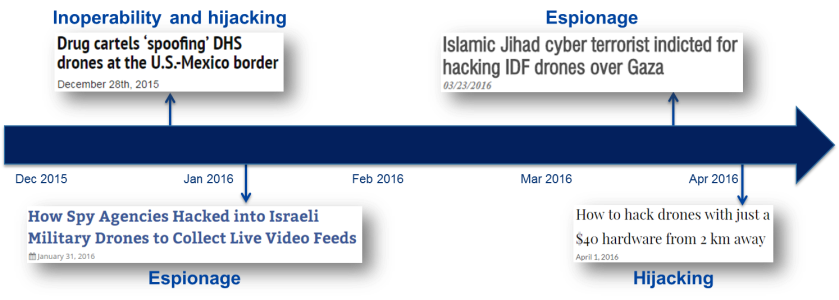
As shown by recent hacks, several professional Unmanned Aerial Vehicles (UAV) used byarmed forces, governments, police departments and the private sector are vulnerable to critical attacks which exploit both technical vulnerabilities and design flaws. This can lead to UAVs being spied on, made inoperable or controlled by the attacker unbeknownst to the UAV’s owner.

From a military intelligence perspective, it’s a godsend to gather valuable information. The GCHQ/NSA joint Operation Anarchist[1] during which Israeli drones’ scrambled video signals were intercepted and reconstructed, providing the US and UK a clear view of Israeli drones’ position, movements, payload and video footage is the perfect example. The Operation Anarchist – which started in 1998, lasted more than a decade and was disclosed only in late December 2015 – was run from the Troodos Mountains, Cyprus, from where encrypted video signals between Israeli drones and their bases were intercepted and unscrambled using open-source software tools.
The obvious drawback however for governments is that the same techniques can be used against them and become a serious threat, particularly when it comes to State security and notably for law enforcement agencies. While entry-level drones present vulnerabilities, their main purpose seems to be to reduce cost. IBM researcher Nils Rodday proved that high-end drones were also vulnerable when he studied professional quadcopters used by law enforcement agencies in the context of his Master’s Thesis[2] in 2015. He showcased the results of the hacks during the RSA Conference 2016[3]. He also analyzed the quadcopters and discovered that the on-board chips lacked encryption implementation[4] which allowed him to hijack the drone by emulating the commands sent to the UAV through the controlling application. Furthermore, he took advantage of the weak encryption (WEP) used to cipher the link between the drone and its controller.

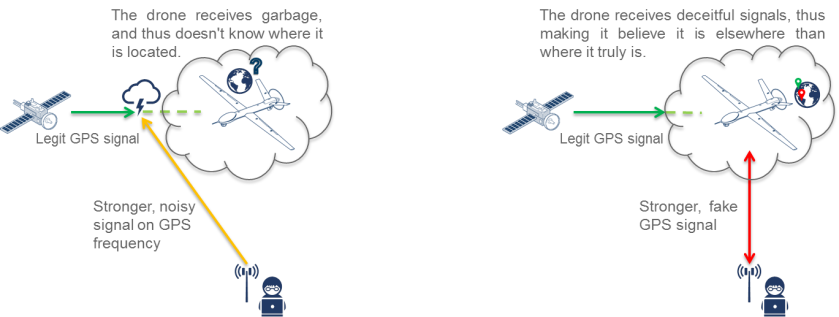
In addition, concerns regarding homeland security have emerged, as shown by the case of the Mexican drug cartel who, in late December 2015, managed to control the US Customs and Border Patrol (CBP) drones’ movements[5]. This allowed the cartel to reroute the US CBP’s drones and to illegally cross the US-Mexican border, enabling them to smuggle drugs and people without being detected. The cartel used GPS jamming and GPS spoofing techniques which respectively disrupted the Command and Control (C&C) link, preventing the drone from receiving GPS signals, overriding legitimate ones and replacing them with fake ones, thus making it deviate from its original route.
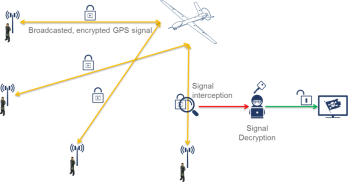
Moreover, warfare methods continually evolve and actors integrate new technologies in their arsenal, leveraging on them during actual conflict as evidenced by the recent hack of the Israeli Defense Forces’[6] (IDF) drone surveillance system. The hack was perpetrated by a member of the Islamic State who gained access to HD footage from IDF’s drones hovering above the Gaza Strip for at least 2 years, starting in 2012 but potentially up until the arrest in February 2016. As a matter of fact, using only commonly available tools such as a satellite dish and a radio receiver[7], the hacker was able to intercept IDF’s drones’ video streams and managed to decode them, thus providing the Islamic State with a clear view of IDF’s drones video footage.
As evidenced by the aforementioned examples, attacks take place in several heterogeneous contexts and originate from actors belonging to different domains and with different levels of skill. In all the above mentioned cases, these events highlight weaknesses and vulnerabilities in the technologies used by UAVs along with flaws in the processes that were put in place by the victims regarding information handling. Military, law enforcement and governments are critical targets; however, the private sector is not spared as drones are being considered more widely by corporations for new services – Amazon Prime Air is a great example of that and may result in very annoying hacking opportunities to say the least. Consequences may be a matter of national security and public safety, therefore implementing best practices, setting up proper countermeasures – such as spread spectrum modulation in the case of signal jamming – and using state-of-the-art technologies proves itself crucial, yet being aware of the threat landscape one’s facing along with one’s own kill-chain is fundamental in order to avoid and mitigate such cases at best.
Vulpoid
References:
[1] https://theintercept.com/2016/01/28/israeli-drone-feeds-hacked-by-british-and-american-intelligence/
[2] https://www.jbisa.nl/download/?id=17706129
[3] https://www.rsaconference.com/writable/presentations/file_upload/ht-w03-hacking_a_professional_police_drone.pdf
[4] http://securityaffairs.co/wordpress/45848/hacking/how-to-hack-drones.html
[5] http://www.nationalsecurity.news/2015-12-28-drug-cartels-spoofing-dhs-drones-at-the-u-s-mexico-border.html
[6] http://www.ynetnews.com/articles/0,7340,L-4782430,00.html
[7] http://www.thedailybeast.com/articles/2016/03/25/how-islamic-jihad-hacked-israel-s-drones.html


One comment