After taking down the Xbox Live and the Playstation Network gaming services, the Lizard Squad group came again in the spotlight after the leak of a database of their LizardStresser not-so-new booter (a service providing Distributed Denial of Service or DDoS against payment). The breach occurred mid-January and resulted in the release of a 19 MB sql file containing the database content, consisting of about 150000 lines. We analyzed the data, focusing on targets and on attacks. After a bit of scripting, behold!
First, here’s a summary of the quantities of attacks and of attackers, showing that only 1.95% of the registered users actually used the service and launched at least one attack:
Registrations vs. usage
The low registration/usage ratio can be explained by the cost of the service: before being allowed to perform any attack, one had to pay a minimum of USD 5.99 — according to the Plans table — or use the free booter , which was most likely very limited and apparently absent from the logs. This might have been an obstacle for many since the Comments table abounds of users asking for free trials.
Targets’ location
From the statistics listed above, 81 countries were affected. The top 5 are shown in the chart below, alongside with Switzerland, ranking 19th:
The US were the main target, with 43% of the targeted IP addresses located there. The next most targeted country is Germany with 9% of the attacks; about 5 times less than the US. Most significant internet services (such as gaming services) being located in the US, these figures aren’t surprising. Given this, the repartition seen above is not really astonishing. Less than 1% of the targets are located in Switzerland, which again isn’t stupefying considering the country’s size and online activity.
Targets’ activity sectors
To categorize targets per activity sectors, we didn’t check each target manually but rather used a somewhat heuristic method consisting in defining a few sets of keywords and then searching for them inside the Description field of each target IP’s Whois entries :
In the US, we were able to identify about half of the attacks belonging to generic Corporations rather than specific activity sectors. A quarter of all attacks were aimed at Telecommunications and almost another quarter at Webhosting companies. The Corporation category includes corporation-related entities not specifically related to any other category. For instance, “EXAMPLE WEBHOST Corp.” would go into Webhosting but “EXAMPLE Corp.” would go into Corporations since nothing allows us to tell more about its activities.
The discrepancy between targets in the US and Germany or Switzerland doesn’t necessarily mean that targets were country-oriented.
In the US Corporations are the main target, followed by Webhosting and Telecommunication. Corporations include Facebook and Google; most likely their web services but we didn’t investigate further to try to find out which ones.
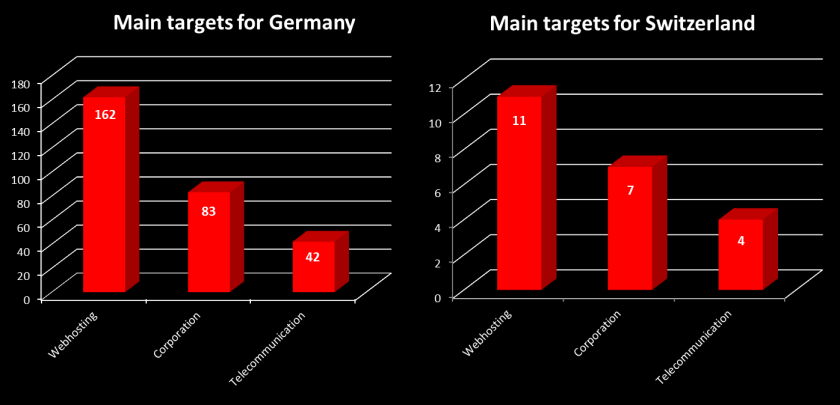
In Germany — second most targeted country — the situation is reversed: Webhosting is the main target and then Corporation is closely followed by Telecommunication. When we compare Germany’s attack distribution with a country not in the top 5, such as Switzerland, we observe that their distribution of activity sectors is similar.
Top IPs attacked
Looking at IP addresses, the most attacked ones were 208.74.65.10 and 206.223.150.26 — respectively 1’468 and 1’130 times, which represents about 9% and 7% of all attacks. Further investigation shows that they’re telecommunications/hosting companies, so nothing shocking about their high attack count given what we observed and concluded before. In addition, they were attacked on ports 80 and 443, which are HTTP and HTTPS ports.
Attackers
These two IP addresses were attacked by the same user every time: ryanbrogan. He’s responsible for 3’034 attacks which targeted 20 IP addresses on 5 ports in 8 countries. Each one of the targeted IP addresses corresponds to an ISP, hosting company, or VPS/Dedicated servers’ provider, meaning that he most likely targeted only individuals and their websites. 78.8% of his attacks were on port 80.
If we review the time and duration of his attacks, we observe a range between the duration of his attacks of virtually 0 second (one single attack) to almost 3 days for his second top attack (he launched attacks on the same target restlessly for almost 3 days). In fact, for the most targeted IP address, only 22 attacks have more than 120 seconds between them, leaving him with more than 1400 attacks — each of them during 100 seconds, which means a total of about 39 hours — to launch within an interval of 2 minutes between each attack.
ryanbrogan was therefore most likely using a bot to launch his attacks (or has sharp reflexes and a lot of patience), explaining such a great amount. In addition, this method allowed him to pay only for the cheapest plan and launch burst attacks. When comparing ryanbrogan’s attack rate with the second most active user, najim1999, we see that ryanbrogan was the only user having operated in such a way. As a matter of fact, najim1999 launched 564 attacks (about 3.5% of all attacks) on 303 IP addresses and attacked his “top” target 18 times within a week, which is far from ryanbrogan’s performance…
The remaining users used similar patterns to najim1999’s confirming that ryanbrogan was an exception. He had an impact but it seems that he attacked mostly individuals, proving that his goal was not money but more likely fun, revenge or both.
Conclusion
This short analysis of LizardStresser showed that the service was used by what seems like neophytes seeking nothing but fun except for one user; hence, it did not represent a real threat. Still, it had the potential to cause massive damages and it is therefore of great importance to remain aware and to proactively take measures countering a potential heavier use of such services: identifying and monitoring relevant hacker teams allows us to stay informed of potential threats and to take the best decisions. Besides, the potential financial gain is not negligible: cross-matching the Plans and Logs tables suggests approximately 4000 USD earned by the Lizard Squad during a period of about 2 weeks, representing about 16 USD per active user (these numbers are based on the monthly option, which is the cheapest and was probably most often chosen by users). Given this, it wouldn’t be surprising that these services came to multiply, as well as their users, stressing once again the importance of an efficient strategy, namely the investment in adequate resources and skills providing the proper means to counter such attacks.
Vulpoid






Nice post. I learn something totally new and challenging on blogs I stumbleupon every day.
It will always be interesting to read content from other writers and practice a little something
from other web sites.
Awesome things here. I am very happy to peer your post.
Thanks a lot and I’m having a look forward to contact you.
Will you kindly drop me a mail?