After a long process started in 2016, today NIST announced the first standardized cryptographic algorithms designed to protect IT systems against future quantum attacks. Here
After a long process started in 2016, today NIST announced the first standardized cryptographic algorithms designed to protect IT systems against future quantum attacks. Here

Infrastructure-as-Code (IaC) is great. It allows teams to deploy infrastructure quickly in a consistent and repeatable manner and when coupled with a proper CI/CD process
Pretty Good Privacy (PGP) and the open source implementation GNU Privacy Guard (GPG) are encryption solutions following the OpenPGP standard. Even if GPG has been

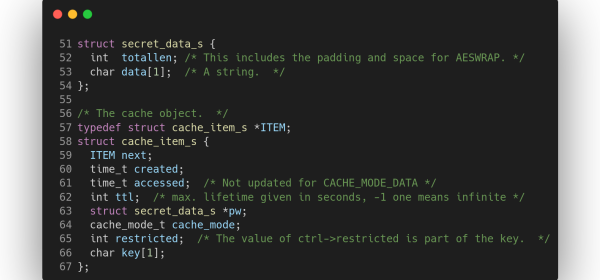
This bulletin was written by Eric Dodge of the Kudelski Security Threat Detection & Research Team Summary Microsoft has recently mitigated a vulnerability that was

This bulletin was written by Michal Nowakowski of the Kudelski Security Threat Detection & Research Team Summary On May 27th, 2022, threat researchers identified a
This bulletin was written by Travis Holland and Eric Dodge of the Kudelski Security Threat Detection & Research Team Executive Summary On May 18th, 2022,