Written by Mark Stueck and Scott Emerson of the Kudelski Security Threat Detection & Research Team CVE-2023-27532: Unauthenticated Access to Cleartext Credentials Possible Through Veeam Backup
Written by Mark Stueck and Scott Emerson of the Kudelski Security Threat Detection & Research Team CVE-2023-27532: Unauthenticated Access to Cleartext Credentials Possible Through Veeam Backup
Written by Michal Nowakowski of the Kudelski Security Threat Detection & Research Team UPDATE – February 14th 2023 After the first wave of ESXiArgs ransomware

Written by Harish Segar of the Kudelski Security Threat Detection & Research Team Summary On December 13, 2022, The U.S. National Security Agency (NSA) release

Written by Mark Stueck of the Kudelski Security Threat Detection & Research Team Summary On Tuesday, December 13th, Microsoft reclassified a previously acknowledged information disclosure
This bulletin was authored by Mark Stueck of the Kudelski Security Threat Detection & Research Team. Summary On December 12th, 2022, Fortinet disclosed the existence
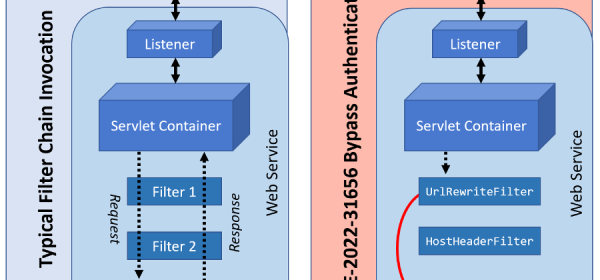
Proof-of-Concept (PoC) exploit recently released by security researchers. VMware recommends patching affected systems immediately. Executive Summary On August 2nd, 2022, VMware issued an advisory (VMSA-2022-0021)