In fall 2012, I proposed to organize an open competition in order to develop a new crypto standard for hashing passwords—be it to protect users’ credentials in web services, derive keys for disk encryption schemes, or to log in your operating system. That’s how the Password Hashing Competition (PHC) started.
Almost three years later, I’m happy to announce the first Password Hashing Competition winner, Argon2. Since Monday, specifications and public-domain code are available at https://password-hashing.net/#argon2, and on a GitHub repository:
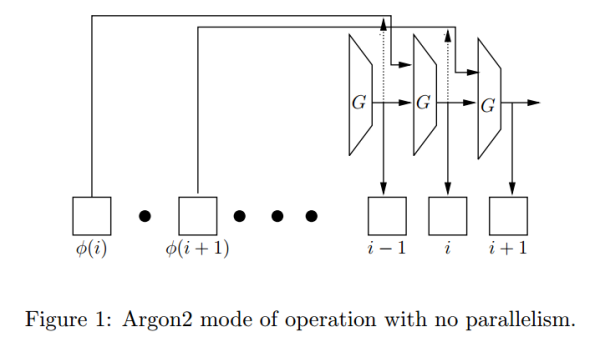
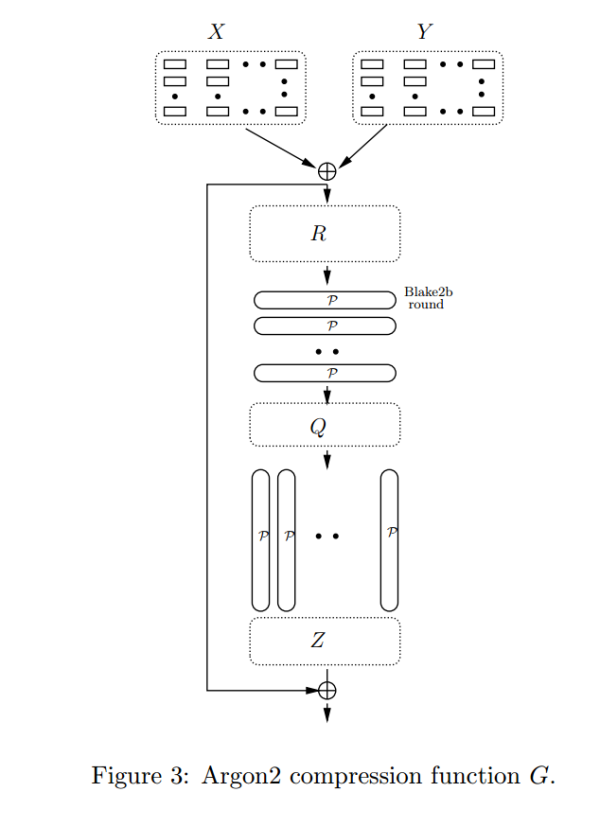
Argon2 was designed by a team from Luxembourg University, led by Dmitry Khovratovich—previously known for discovering the best cryptanalytic attacks on AES. To defeat brute force and dictionary attacks, Argon2 can be tuned to use as much computation and memory as the application tolerates, and support multi-threading. It uses the BLAKE2 hash algorithm to securely scramble input data (password and salt). These excerpts from the specs will give you a glimpse of how Argon2 works at a higher level:
You’re welcome to test our reference C code and to report any bugs you find—we’ve worked hard to test it, but it’s unlikely to be totally bug free yet. The code should compile on Linux, BSD, OS X, and Windows platforms. Let us know if you write bindings for other languages, we’ll mention them on the website.
As PHC finishes, I’d like to thank everyone: designers, panel members, mailing list posters, testers. Hope we’ve done something useful!